The New Fraud Frontier: Why Businesses Must Rethink Identity Verification

Many fraudsters today are no longer just criminals – they’re technologists wielding powerful artificial intelligence (AI) as their primary weapon. As fraud techniques evolve, businesses are becoming increasingly vulnerable to sophisticated adversaries. With the rising wave of AI-powered fraud, traditional fraud prevention methods, which heavily emphasise Know-Your-Customer (KYC) processes, are struggling to keep pace. Fraudsters […]
Bridging the cybersecurity skills gap with automation and collective defence

In an era of rapidly advancing cyber threats, organisations are struggling to keep up with the growing demand for skilled cybersecurity professionals. With the talent shortage showing no signs of easing, businesses must rethink their approach to security operations, argues Dan Bridges, Technical Director – International, Cyware. Organisations around the world are battling to fill […]
Is it Time to Accept that the Current Role of the CISO Has Failed?

It has become too complex to carry for the profile of people it attracts The role of the Chief Information Security Officer (CISO) has been in existence for the best part of the last 30 years. Infosec legends say that it was first created for Steve Katz at Citibank in 1995, and indeed it has […]
How can businesses prepare for the UK’s Cyber Security and Resilience Bill?

As cyber threats become more frequent, sophisticated and damaging, UK businesses are being urged to prepare now for the Government’s forthcoming Cyber Security and Resilience Bill. The proposed legislation – outlined in a Government policy statement on 1st April 2025 – aims to significantly expand the UK’s cyber security regulatory framework. Jonathan says, “The Bill will […]
Collaboration is key to gaining the upper hand in the shifting battlefield of cyberwarfare

Thirty-five years ago, the future of cybersecurity was changed forever. Delivered on the humble floppy disk, the AIDS Trojan marked the introduction of ransomware to the world. The program, while masquerading as information on AIDS, instead encrypted the computer files and charged a ransom of $189 to decrypt them. In 1989, owning a personal computer was a […]
If ransomware payments become illegal, how can your business prepare?
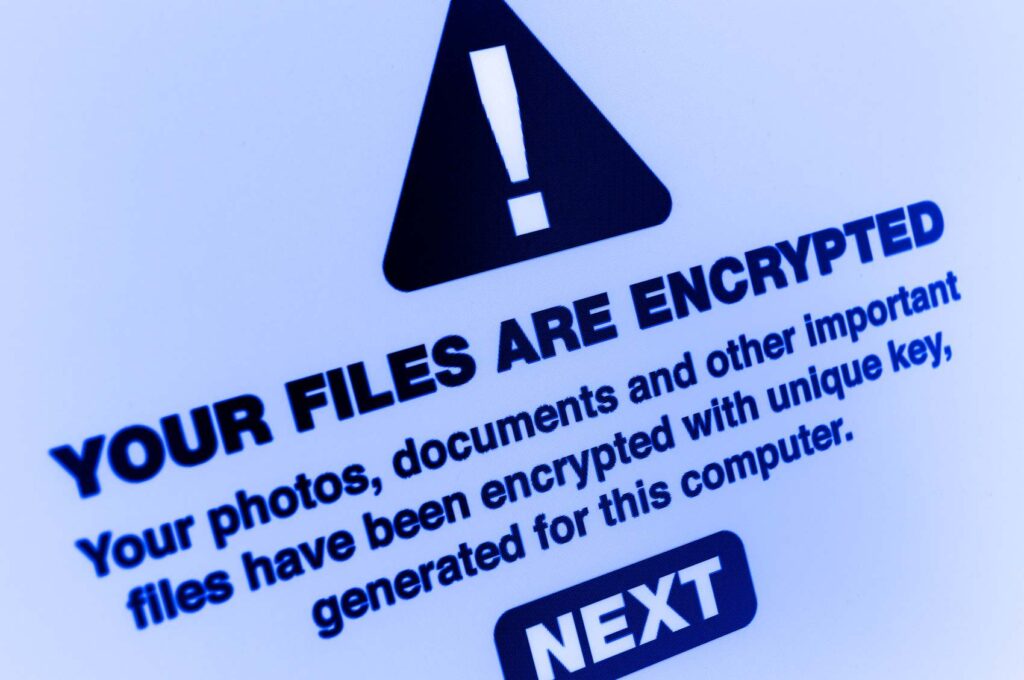
Earlier this year, the UK government opened proposals on a set of world-leading proposals to protect businesses against ransomware threats. The proposals would make it illegal for public sector organisations to make ransomware payments and increase reporting requirements for all victims. The goal of this has been to undermine the ransomware business model, ultimately making […]
Stronger Together: Why IT and Security Collaboration is Business Critical

As UK businesses accelerate their digital transformation, the move to cloud-based and hybrid work environments has introduced new layers of complexity in IT management and security. While these advancements offer increased flexibility and scalability, they also create opportunities for cybercriminals to exploit gaps in an organisation’s security posture. One of the most pressing issues is […]
Cybersecurity is Not Working: Time to Try Something Else

The bottom-up approaches most have been pushing for 20 years around cybersecurity have simply failed I think it is time to accept that the role of the CISO, in its historical construction, was never born out of a positive and proactive management decision. It was very rarely created – at first – in response to […]
With AI-Powered Cyber Threats on the Rise, Businesses Need Clarity

Whether we like it or not, AI now pervades our world. From public and private sectors to personal life, this powerful technology surely poses potential risks, but it’s also the catalyst for untold opportunities. As the UK advances its AI regulatory framework, it is considering transforming voluntary agreements with AI developers into legally binding commitments […]
Inside a Cyberattack: How Hackers Steal Data

The truth about cybersecurity is that it’s almost impossible to keep hackers outside of an organisation, particularly as the cybercrime industry becomes increasingly sophisticated and their technology more advanced. Furthermore, once a hacker has broken through an organisation’s defences, it is relatively easy to move within the network and access information without being detected for […]